Did you ever need to find in your Office 365 tenant : what objects are using a specific email address or UserPrincipalName ? what objects are preventing an AD account syncing ? where are them located in your tenant : in Users, in Contacts or in Deleted users ?
Manage Office 365 Roles membership
Hello, I'am sharing with you how to manage Roles in Office 365 using PowerShell. It can be helpful for Office 365 administrators.
Permanently remove a guest user in Office 365
Permanently remove a guest user in Office 365
Allocate licenses in bulk to your Office 365 users (Option 1 : Using PowerShell)
As an Office 365 IT professional, you may need to allocate license to users. There are several ways for doing that. Here, I will show you two ways to achieve your goal.
Get your Office 365 users licenses
If ever, you asked yourself one day, how to quickly view the Office 365 licenses configuration for a group of users in your organization, here is a script that can help you achieve that goal.
Export Office 365 users and their Licenses configurations
Export Office 365 users and their Licenses configurations
Rajouter des utilisateurs dans un groupe AD à partir d’un fichier .CSV
Hello, je partage ce petit script qui pourrait vous être utile si vous souhaitez rajouter des utilisateurs (100, 1000...) en bloc à un groupe AD.
Importer une VM Hyper-V dans Microsoft Azure
Dans le précédent article, nous avons vu comment installer Hyper-V sous Windows 10 et créer une VM. Intéressons-nous maintenant à son importation dans Microsoft Azure. Créer un compte de test Microsoft Azure si vous n'en avez pas encore. Etape 1 : Préparation de la VM Hyper-V pour son importation dans Microsoft Azure Nous allons syspreper la... Continue Reading →
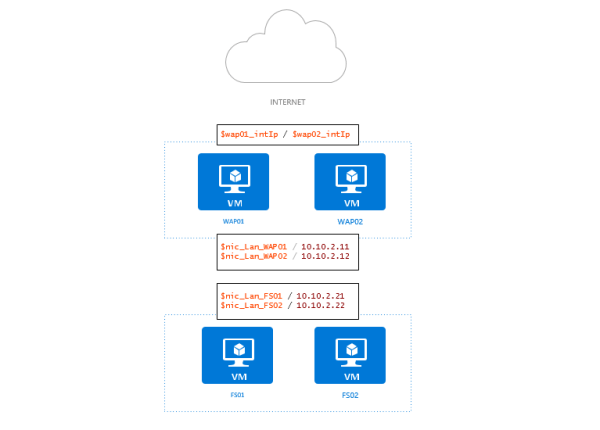
Installer des Machines Virtuelles à l’aide d’Azure PowerShell
Déployer des machines virtuelles à l'aide de PowerShell pour Azure